What is Google Titan Security Chip and How it Works?
Announced in March atGoogle Cloud Next '17, the Google Titan securitychip is another edifice block in Google's effort to dial upwards its security credentials and narrow the gap with its competitors – primarily AWS and Microsoft Azure. Subsequently testing the flake in their data centers for quite a while now, Google recently announced its technical details. So, if you lot have been coming across news of Google's Titan security fleck and wondering what is information technology all about. Well, in this commodity, I will get over what the Google Titan security bit is, how does information technology work, and everything else that you need to know about it.
What is the Titan Security Chip?
In the simplest of words, Titan is a security fleck that prevents the blazon of attacks where government spies intercept hardware and insert a firmware implant. Currently, the attackers do this mainly by exploring firmware vulnerabilities to overcome operating system defenses and installing rootkits that can persist fifty-fifty after the operating system has been reinstalled.
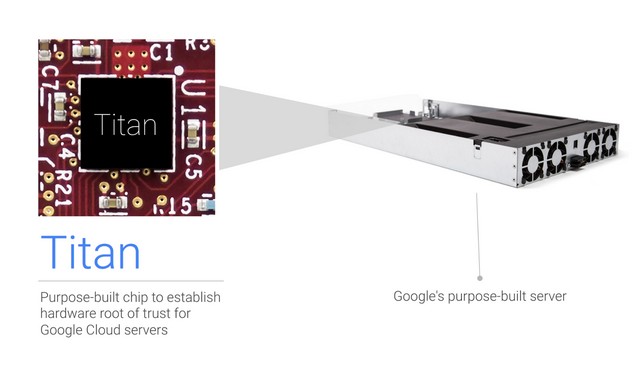
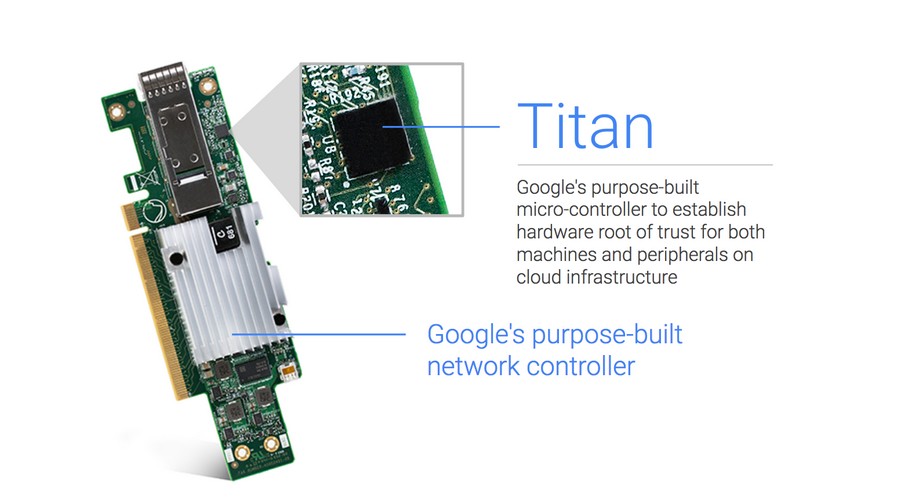
Titan is a office of Google Deject Platform (GCP) which is designed, built, and operated with the goal to protect customers' code and data. The fleck is a secure, low-power micro-controller created to ensure that systems e'er kicking from the last known good state. The chip is of the size of a small stud earring and has already been installed in many of the computer servers and network cards that populate Google's massive data centers.
When the fleck was showtime unveiled dorsum in March of this yr, Google planned to employ the processor to give each of its servers an private identity. As of today, Google currently uses the Titan security fries to protect the servers running its own services like Google Search, Gmail, and YouTube.
What Does the Titan Security Chip Comprise of?
The machines in Google'due south information centers have multiple components including CPUs, RAM, BMC, Network Interface Controller (NIC), boot firmware, kicking firmware flash, and persistent storage. These components interact with each other systematically to kick the machines. To protect this boot procedure, Google uses secure boot which relies on a combination of an authenticated boot firmware and a bootloader, along with digitally signed boot files, to provide the desired security measures.
Titan is a specially designed bit that not simply meets these expectations merely besides provides two important additional security properties – remediation and first-instruction integrity. The flake communicates with the main CPU via the SPI bus and interposes between the boot firmware wink of the components like BMC or PCH. This allows it to observe every byte of the kick firmware.
To attain the security measures that Titan promises, it comprises of several components. Some of the salient ones are mentioned beneath.
- A secure awarding processor
- A cryptographic co-processor
- A hardware random number generator
- A sophisticated central hierarchy
- An embedded static RAM (SRAM)
- An embedded flash
- A read-only memory block
- Serial Peripheral Interface (SPI) bus
- Baseboard Management Controller (BMC) or Platform Controller Hub (PHC)
How Does the Titan Security Chip Piece of work?
The first step in the working of the Titan security flake is execution of code by its processors. This is done immediately after the host machine is powered up. Then the fabrication process lays downward an immutable code that is trusted implicitly and is validated at every fleck reset. Afterwards, the bit runs a self exam that is built into its retention. This happens every time information technology boots to ensure that all the retentiveness, including ROM, has not been tampered with.
The next step is to load Titan's firmware. Even though this firmware is embedded in the on-chip flash retention, the Titan kicking ROM does not trust it blindly. Instead, it verifies Titan's firmware using public key cryptography and mixes the identity of this verified code into Titan'southward fundamental hierarchy. Finally, the boot ROM loads the verified firmware.
Once the Titan chip boots its own firmware securely, the contents of the host's boot firmware flash are and then verified using public cardinal cryptography. While this verification is nether process, Titan can gate the access for PCH/BMC to the boot firmware flash. Now when the process finally gets completed, the chip sends a signal to release the balance of the auto from reset. This betoken provides Google Cloud Platform with the information well-nigh what kick firmware and OS are being booted on their motorcar from the very first education. Google Cloud Platform also learns about the microcode patches that may have been fetched before the boot firmware'south first instruction.
Finally, the Google-verified kicking firmware configures the automobile and loads the bootloader. This later verifies and loads the operating system.
Why the Demand for Titan Security Flake?
As most network hardware and servers were made overseas, data center operators working for Google Cloud Platform were concerned nigh the possibility of nation-state hackers or cyber criminals compromising these devices before aircraft them. Google'south Titan flake addresses these concerns through its continual checks which provide boosted security to the cloud computing hardware. This allows the visitor to maintain a level of understanding in their supply chain that they otherwise wouldn't have.
Another reason why installing the Titan security bit in computer servers is the countering new firmware attacks which tin can target re-writable firmware chips. These could either exist BIOS chips or hard bulldoze controllers.
How Does the Titan Security Flake Benefit Google?
There are two primary ways in which the Titan security fleck benefits Google. First is the security bespeak-of-view and second is the competitive point-of-view.
From the security bespeak-of-view, the Titan chip benefits Google in the post-obit three means:
- Information technology provides a hardware-based root of trust that establishes a strong identity of a car. This helps Google make important security decisions and validate the health of the system. As a result, this ensures an irreversible audit trail of any changes made.
- The tamper-axiomatic logging capabilities aid identify deportment performed past an insider with root access.
- The fleck offers integrity verification of firmware and software components.

From the competitive perspective, Google Cloud Platform currently has a 7% global deject market share. This makes it stand up third to the likes of Amazon Web Services (AWS) (41% marketplace share) and Microsoft Azure (13% market share). With the new Titan chip, Google is looking to ready itself autonomously from its competitors and bring more security-focused companies to its cloud computing platform. This is an important movement as, co-ordinate to Gartner, the worldwide cloud computing market is worth nearly $50 billion.
Equally a consequent do good, Google has also adult an end-to-end cryptographic identity system based on Titan. This tin can further human activity every bit the root of trust for varied cryptographic operations in their data centers.
SEE ALSO: What is Bluetooth Mesh Networking and How Information technology Works?
Will the Titan Security Chip Really Assistance Google?
While Google Cloud Platform currently falls behind its competitors, peculiarly AWS, the Titan security chip does sound similar a great deal for them. With its impressive test results, it all comes down to whether or not the flake will help Google Deject Services stand out from the others in the longer run. Personally, I am very interested too see how things will turn out. What about you lot? Do let me know your thoughts on this in the comments section below.
Source: https://beebom.com/what-is-google-titan-security-chip/
Posted by: gideongallembey.blogspot.com


0 Response to "What is Google Titan Security Chip and How it Works?"
Post a Comment